Key Insights
The Internet of Things (IoT) Identity and Access Management (IAM) market is poised for explosive growth, reaching an estimated $11.3 billion in 2025. This remarkable expansion is driven by a projected Compound Annual Growth Rate (CAGR) of 24.8% from 2019 to 2033. The escalating adoption of IoT devices across diverse industries, coupled with the increasing sophistication of cyber threats targeting these connected ecosystems, is a primary catalyst. Organizations are recognizing the critical need to secure their IoT deployments, ensuring that only authorized entities can access and control devices and the data they generate. This fundamental security imperative is fueling demand for robust IAM solutions specifically designed for the unique challenges of IoT environments, including device provisioning, authentication, authorization, and ongoing lifecycle management. The market's trajectory indicates a significant shift towards proactive security measures rather than reactive incident response.

iot identity access management iam Market Size (In Billion)

The IoT IAM market's rapid ascent is further propelled by emerging trends such as the widespread adoption of AI and machine learning for anomaly detection and predictive security, the increasing demand for zero-trust architectures in IoT deployments, and the growing regulatory landscape that mandates enhanced data security and privacy for connected devices. These factors are collectively shaping a dynamic market where innovation in authentication protocols, credential management, and policy enforcement is paramount. While the market's growth is robust, potential restraints include the complexity of integrating IoT IAM solutions with existing legacy systems, the shortage of skilled professionals in IoT security, and the initial cost of implementing comprehensive IAM frameworks. Nevertheless, the overwhelming need to mitigate the risks associated with insecure IoT devices and ensure the integrity of operations will continue to drive substantial investment and innovation in this vital sector.

iot identity access management iam Company Market Share

Comprehensive Report: IoT Identity and Access Management (IAM) Market Analysis (2019-2033)
This in-depth report provides a detailed analysis of the global IoT Identity and Access Management (IAM) market, spanning a study period from 2019 to 2033, with a base and estimated year of 2025 and a forecast period from 2025 to 2033. The report offers critical insights for industry stakeholders, including manufacturers, solution providers, investors, and policymakers, covering market structure, competitive dynamics, industry trends, dominant markets, product innovations, segmentation, key drivers, challenges, leading players, and future market outlook. The analysis encompasses both global and United States markets, with specific attention to various applications and types within the IoT IAM ecosystem.
IoT Identity Access Management IAM Market Structure & Competitive Dynamics
The global IoT Identity and Access Management (IAM) market exhibits a moderately concentrated structure, characterized by the presence of established IAM vendors and a growing number of specialized IoT security startups. Innovation ecosystems are rapidly evolving, driven by the escalating need for robust device authentication, authorization, and lifecycle management for the burgeoning Internet of Things. Regulatory frameworks, though still developing in some regions, are increasingly emphasizing data privacy and security, compelling organizations to adopt comprehensive IoT IAM solutions. Product substitutes include traditional IT IAM solutions retrofitted for IoT, but these often lack the scalability and specific features required for the vast and diverse IoT landscape. End-user trends showcase a strong demand for automated provisioning, granular access controls, and continuous monitoring to mitigate the expanding attack surface of connected devices. Mergers and acquisitions (M&A) activities are on the rise as larger security players seek to bolster their IoT capabilities. For instance, M&A deal values are projected to reach over $10 billion by 2028, reflecting the strategic importance of this sector. Market share distribution varies significantly, with leading players holding substantial portions, but smaller, innovative firms are carving out niches. The continuous evolution of the threat landscape also fuels the need for proactive and adaptive IAM strategies.
IoT Identity Access Management IAM Industry Trends & Insights
The IoT Identity and Access Management (IAM) industry is poised for substantial growth, driven by the exponential proliferation of connected devices across diverse sectors. Key market growth drivers include the increasing adoption of smart technologies in industrial automation, healthcare, smart cities, and consumer electronics, all demanding robust security for billions of connected endpoints. Technological disruptions such as the rise of AI-powered threat detection, decentralized identity solutions leveraging blockchain, and the integration of zero-trust architectures are fundamentally reshaping how IoT devices are secured and managed. Consumer preferences are increasingly shifting towards privacy-conscious solutions, compelling manufacturers and service providers to prioritize secure data handling and transparent access controls. The competitive dynamics are intensifying, with a blend of established cybersecurity giants and agile startups vying for market dominance. The average annual growth rate (CAGR) for the IoT IAM market is conservatively estimated at xx% for the forecast period, with market penetration expected to reach over 70% in enterprise deployments by 2030. The growing sophistication of cyberattacks targeting IoT devices, ranging from botnet recruitment to critical infrastructure disruption, is a primary impetus for enhanced IAM investments. Furthermore, the increasing regulatory pressure worldwide, mandating stronger security measures for connected devices, acts as a significant catalyst for market expansion. The development of lightweight yet highly secure authentication protocols tailored for resource-constrained IoT devices is another critical trend. The convergence of IT and OT (Operational Technology) security necessitates IAM solutions that can bridge these traditionally separate domains, offering unified visibility and control. The adoption of cloud-based IAM platforms is also accelerating, providing scalability and flexibility for managing vast IoT deployments. The evolving landscape of device heterogeneity, from simple sensors to complex industrial machinery, requires adaptable IAM frameworks capable of handling diverse authentication mechanisms and access policies. The projected market size for IoT IAM solutions is expected to exceed $20 billion globally by 2028, underscoring its critical importance in the digital economy.
Dominant Markets & Segments in IoT Identity Access Management IAM
The North America region, particularly the United States, currently dominates the global IoT Identity and Access Management (IAM) market. This dominance is driven by several key factors, including a mature technological infrastructure, significant investments in IoT development and deployment across various industries, and stringent data security and privacy regulations. The US government's focus on cybersecurity initiatives and the presence of leading technology companies headquartered in the region further bolster its leading position.
Key Drivers of Dominance in the United States:
- Robust Regulatory Frameworks: The US has well-established regulations like HIPAA, GDPR (though primarily EU, its influence extends to US companies handling EU data), and NIST guidelines that mandate strong data protection and access control, driving the adoption of advanced IoT IAM solutions.
- High IoT Adoption Rates: Industries such as healthcare, manufacturing, smart cities, and logistics in the US have demonstrated exceptionally high adoption rates for IoT technologies, creating a substantial demand for comprehensive IAM solutions.
- Technological Innovation Hubs: The presence of major technology hubs and venture capital funding fuels rapid innovation in cybersecurity, including IoT IAM, leading to the development and deployment of cutting-edge solutions.
- Enterprise Investment: Large enterprises in the US are prioritizing cybersecurity investments, recognizing the critical need to secure their expanding IoT footprints against evolving threats.
Within the Application: segments, Industrial IoT (IIoT) and Healthcare IoT are emerging as particularly dominant areas. IIoT's application in smart manufacturing, predictive maintenance, and supply chain optimization involves a vast number of connected devices, each requiring secure authentication and access. The critical nature of industrial operations necessitates robust IAM to prevent operational disruptions and ensure safety. Healthcare IoT, encompassing remote patient monitoring, connected medical devices, and hospital asset tracking, demands stringent access controls to protect sensitive patient data (PHI) and ensure the integrity of medical devices, making it a high-priority segment for IoT IAM solutions.
Regarding Types: of IoT IAM solutions, Device Identity and Authentication holds a significant market share. This segment focuses on securely identifying and authenticating each individual IoT device connecting to a network. This includes certificate-based authentication, multi-factor authentication for devices, and secure credential management. The sheer volume of devices necessitates scalable and automated solutions for this critical function. Following closely is Authorization and Access Control, which defines and enforces what actions authenticated devices and users can perform within the IoT ecosystem. This granular control is paramount for preventing unauthorized access and data breaches.
IoT Identity Access Management IAM Product Innovations
Recent product innovations in IoT Identity and Access Management (IAM) are centered on enhancing scalability, automating device onboarding, and strengthening security against sophisticated threats. Advancements in machine learning and AI are being integrated to enable behavioral analytics for device anomaly detection and proactive threat identification. Innovations include the development of lightweight, resource-efficient authentication protocols for constrained IoT devices and the introduction of zero-trust IAM frameworks specifically designed for IoT environments. Solutions are also emerging that offer unified identity management across both IT and OT systems, providing end-to-end visibility and control. Competitive advantages are gained through seamless integration with existing security infrastructure, comprehensive device lifecycle management capabilities, and adherence to evolving industry standards and regulations.
Report Segmentation & Scope
This report segments the IoT Identity and Access Management (IAM) market by various Application: categories, including Industrial IoT (IIoT), Healthcare IoT, Smart Cities, Connected Vehicles, Consumer IoT, and others. Each application segment is analyzed for its unique IAM requirements, market size projections, and competitive landscape. Furthermore, the report segments the market by Types: of IAM solutions, such as Device Identity and Authentication, Authorization and Access Control, Identity Lifecycle Management, Access Governance, and Security Analytics. Growth projections for each type are provided, along with insights into their respective market sizes and the key players driving innovation within each category. The scope of this report is to provide a holistic view of the global IoT IAM market, from historical trends to future projections, aiding strategic decision-making for all stakeholders.
Key Drivers of IoT Identity Access Management IAM Growth
The rapid expansion of the Internet of Things (IoT) across all sectors is the primary driver for IoT IAM growth. The escalating volume and diversity of connected devices create a vast attack surface, necessitating robust security measures. Increasing cybersecurity threats and data breaches targeting IoT devices highlight the urgent need for comprehensive identity and access management. Furthermore, stringent government regulations and industry standards mandating data privacy and device security are compelling organizations to invest heavily in IoT IAM solutions. The growing adoption of cloud computing and edge computing also fuels the demand for scalable and flexible IAM platforms that can manage distributed IoT environments.
Challenges in the IoT Identity Access Management IAM Sector
Despite robust growth, the IoT Identity and Access Management (IAM) sector faces several challenges. The sheer scale and heterogeneity of IoT devices present significant deployment and management complexities. Lack of standardization in IoT security protocols can hinder interoperability between different solutions and devices. The resource constraints of many IoT devices limit the implementation of complex authentication mechanisms. Additionally, the evolving nature of cyber threats requires continuous updates and adaptation of IAM strategies, posing an ongoing challenge for organizations. Regulatory fragmentation across different regions and industries can also create compliance hurdles. The estimated impact of these challenges on market adoption is a potential delay in full-scale implementation for xx% of new IoT projects.
Leading Players in the IoT Identity Access Management IAM Market
- Microsoft
- Amazon Web Services (AWS)
- IBM
- Cisco Systems, Inc.
- Broadcom Inc.
- Hitachi, Ltd.
- Oracle
- Salesforce
- Okta, Inc.
- ForgeRock Inc.
- CyberArk Software Ltd.
- Saviynt Inc.
- Xage Security
- Device Authority
Key Developments in IoT Identity Access Management IAM Sector
- January 2024: Microsoft launched a new suite of IoT security solutions, enhancing its Azure IoT Hub with advanced device identity and access management capabilities.
- November 2023: AWS expanded its IoT security offerings, introducing new features for automated device provisioning and lifecycle management within AWS IoT Core.
- September 2023: IBM announced strategic partnerships to integrate its hybrid cloud IoT IAM solutions with leading industrial automation platforms.
- July 2023: Cisco Systems unveiled a new framework for zero-trust security in industrial IoT environments, emphasizing granular access controls for OT devices.
- April 2023: Google Cloud enhanced its IoT IAM capabilities with AI-driven anomaly detection to proactively identify and mitigate security threats.
- February 2023: A significant merger occurred between a major cybersecurity firm and an IoT security startup, valued at approximately $1.5 billion, to bolster their combined IoT IAM portfolio.
- December 2022: Device Authority launched a next-generation platform for device identity and attestation, designed for ultra-low-power IoT devices.
- October 2022: Okta, Inc. acquired a specialized IoT identity management company, expanding its reach into the rapidly growing IoT security market.
Strategic IoT Identity Access Management IAM Market Outlook
The strategic outlook for the IoT Identity and Access Management (IAM) market remains exceptionally positive, driven by the relentless expansion of connected devices and the increasing imperative for robust cybersecurity. Future growth accelerators include the widespread adoption of AI and machine learning for predictive security and automated threat response, the integration of decentralized identity solutions like blockchain for enhanced trust and transparency, and the continued evolution of zero-trust architectures tailored for the unique challenges of IoT. Opportunities lie in developing comprehensive, end-to-end IAM solutions that seamlessly manage the entire device lifecycle, from secure onboarding to decommissioning. Strategic partnerships and acquisitions will continue to shape the competitive landscape, as companies seek to broaden their offerings and strengthen their market positions. The market is projected to witness sustained innovation, focusing on delivering scalable, flexible, and highly secure IAM solutions to address the evolving needs of a hyper-connected world.
iot identity access management iam Segmentation
- 1. Application
- 2. Types
iot identity access management iam Segmentation By Geography
-
1. North America
- 1.1. United States
- 1.2. Canada
- 1.3. Mexico
-
2. South America
- 2.1. Brazil
- 2.2. Argentina
- 2.3. Rest of South America
-
3. Europe
- 3.1. United Kingdom
- 3.2. Germany
- 3.3. France
- 3.4. Italy
- 3.5. Spain
- 3.6. Russia
- 3.7. Benelux
- 3.8. Nordics
- 3.9. Rest of Europe
-
4. Middle East & Africa
- 4.1. Turkey
- 4.2. Israel
- 4.3. GCC
- 4.4. North Africa
- 4.5. South Africa
- 4.6. Rest of Middle East & Africa
-
5. Asia Pacific
- 5.1. China
- 5.2. India
- 5.3. Japan
- 5.4. South Korea
- 5.5. ASEAN
- 5.6. Oceania
- 5.7. Rest of Asia Pacific
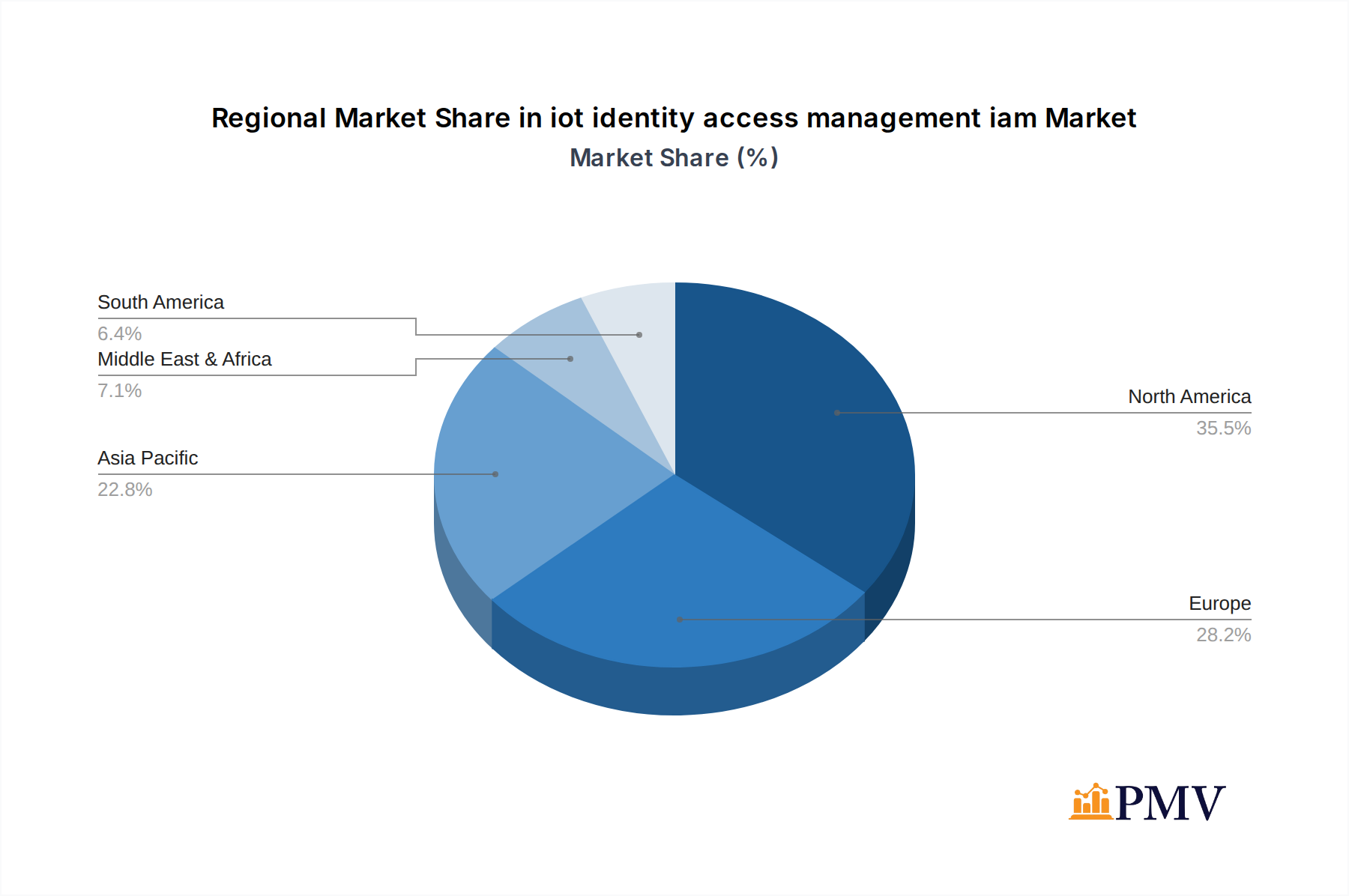
iot identity access management iam Regional Market Share

Geographic Coverage of iot identity access management iam
iot identity access management iam REPORT HIGHLIGHTS
| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of 24.8% from 2020-2034 |
| Segmentation |
|
Table of Contents
- 1. Introduction
- 1.1. Research Scope
- 1.2. Market Segmentation
- 1.3. Research Methodology
- 1.4. Definitions and Assumptions
- 2. Executive Summary
- 2.1. Introduction
- 3. Market Dynamics
- 3.1. Introduction
- 3.2. Market Drivers
- 3.3. Market Restrains
- 3.4. Market Trends
- 4. Market Factor Analysis
- 4.1. Porters Five Forces
- 4.2. Supply/Value Chain
- 4.3. PESTEL analysis
- 4.4. Market Entropy
- 4.5. Patent/Trademark Analysis
- 5. Global iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 5.1. Market Analysis, Insights and Forecast - by Application
- 5.2. Market Analysis, Insights and Forecast - by Types
- 5.3. Market Analysis, Insights and Forecast - by Region
- 5.3.1. North America
- 5.3.2. South America
- 5.3.3. Europe
- 5.3.4. Middle East & Africa
- 5.3.5. Asia Pacific
- 5.1. Market Analysis, Insights and Forecast - by Application
- 6. North America iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 6.1. Market Analysis, Insights and Forecast - by Application
- 6.2. Market Analysis, Insights and Forecast - by Types
- 6.1. Market Analysis, Insights and Forecast - by Application
- 7. South America iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 7.1. Market Analysis, Insights and Forecast - by Application
- 7.2. Market Analysis, Insights and Forecast - by Types
- 7.1. Market Analysis, Insights and Forecast - by Application
- 8. Europe iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 8.1. Market Analysis, Insights and Forecast - by Application
- 8.2. Market Analysis, Insights and Forecast - by Types
- 8.1. Market Analysis, Insights and Forecast - by Application
- 9. Middle East & Africa iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 9.1. Market Analysis, Insights and Forecast - by Application
- 9.2. Market Analysis, Insights and Forecast - by Types
- 9.1. Market Analysis, Insights and Forecast - by Application
- 10. Asia Pacific iot identity access management iam Analysis, Insights and Forecast, 2020-2032
- 10.1. Market Analysis, Insights and Forecast - by Application
- 10.2. Market Analysis, Insights and Forecast - by Types
- 10.1. Market Analysis, Insights and Forecast - by Application
- 11. Competitive Analysis
- 11.1. Global Market Share Analysis 2025
- 11.2. Company Profiles
- 11.2.1. Global and United States
List of Figures
- Figure 1: Global iot identity access management iam Revenue Breakdown (undefined, %) by Region 2025 & 2033
- Figure 2: North America iot identity access management iam Revenue (undefined), by Application 2025 & 2033
- Figure 3: North America iot identity access management iam Revenue Share (%), by Application 2025 & 2033
- Figure 4: North America iot identity access management iam Revenue (undefined), by Types 2025 & 2033
- Figure 5: North America iot identity access management iam Revenue Share (%), by Types 2025 & 2033
- Figure 6: North America iot identity access management iam Revenue (undefined), by Country 2025 & 2033
- Figure 7: North America iot identity access management iam Revenue Share (%), by Country 2025 & 2033
- Figure 8: South America iot identity access management iam Revenue (undefined), by Application 2025 & 2033
- Figure 9: South America iot identity access management iam Revenue Share (%), by Application 2025 & 2033
- Figure 10: South America iot identity access management iam Revenue (undefined), by Types 2025 & 2033
- Figure 11: South America iot identity access management iam Revenue Share (%), by Types 2025 & 2033
- Figure 12: South America iot identity access management iam Revenue (undefined), by Country 2025 & 2033
- Figure 13: South America iot identity access management iam Revenue Share (%), by Country 2025 & 2033
- Figure 14: Europe iot identity access management iam Revenue (undefined), by Application 2025 & 2033
- Figure 15: Europe iot identity access management iam Revenue Share (%), by Application 2025 & 2033
- Figure 16: Europe iot identity access management iam Revenue (undefined), by Types 2025 & 2033
- Figure 17: Europe iot identity access management iam Revenue Share (%), by Types 2025 & 2033
- Figure 18: Europe iot identity access management iam Revenue (undefined), by Country 2025 & 2033
- Figure 19: Europe iot identity access management iam Revenue Share (%), by Country 2025 & 2033
- Figure 20: Middle East & Africa iot identity access management iam Revenue (undefined), by Application 2025 & 2033
- Figure 21: Middle East & Africa iot identity access management iam Revenue Share (%), by Application 2025 & 2033
- Figure 22: Middle East & Africa iot identity access management iam Revenue (undefined), by Types 2025 & 2033
- Figure 23: Middle East & Africa iot identity access management iam Revenue Share (%), by Types 2025 & 2033
- Figure 24: Middle East & Africa iot identity access management iam Revenue (undefined), by Country 2025 & 2033
- Figure 25: Middle East & Africa iot identity access management iam Revenue Share (%), by Country 2025 & 2033
- Figure 26: Asia Pacific iot identity access management iam Revenue (undefined), by Application 2025 & 2033
- Figure 27: Asia Pacific iot identity access management iam Revenue Share (%), by Application 2025 & 2033
- Figure 28: Asia Pacific iot identity access management iam Revenue (undefined), by Types 2025 & 2033
- Figure 29: Asia Pacific iot identity access management iam Revenue Share (%), by Types 2025 & 2033
- Figure 30: Asia Pacific iot identity access management iam Revenue (undefined), by Country 2025 & 2033
- Figure 31: Asia Pacific iot identity access management iam Revenue Share (%), by Country 2025 & 2033
List of Tables
- Table 1: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 2: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 3: Global iot identity access management iam Revenue undefined Forecast, by Region 2020 & 2033
- Table 4: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 5: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 6: Global iot identity access management iam Revenue undefined Forecast, by Country 2020 & 2033
- Table 7: United States iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 8: Canada iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 9: Mexico iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 10: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 11: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 12: Global iot identity access management iam Revenue undefined Forecast, by Country 2020 & 2033
- Table 13: Brazil iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 14: Argentina iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 15: Rest of South America iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 16: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 17: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 18: Global iot identity access management iam Revenue undefined Forecast, by Country 2020 & 2033
- Table 19: United Kingdom iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 20: Germany iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 21: France iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 22: Italy iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 23: Spain iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 24: Russia iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 25: Benelux iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 26: Nordics iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 27: Rest of Europe iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 28: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 29: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 30: Global iot identity access management iam Revenue undefined Forecast, by Country 2020 & 2033
- Table 31: Turkey iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 32: Israel iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 33: GCC iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 34: North Africa iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 35: South Africa iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 36: Rest of Middle East & Africa iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 37: Global iot identity access management iam Revenue undefined Forecast, by Application 2020 & 2033
- Table 38: Global iot identity access management iam Revenue undefined Forecast, by Types 2020 & 2033
- Table 39: Global iot identity access management iam Revenue undefined Forecast, by Country 2020 & 2033
- Table 40: China iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 41: India iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 42: Japan iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 43: South Korea iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 44: ASEAN iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 45: Oceania iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 46: Rest of Asia Pacific iot identity access management iam Revenue (undefined) Forecast, by Application 2020 & 2033
Frequently Asked Questions
1. What is the projected Compound Annual Growth Rate (CAGR) of the iot identity access management iam?
The projected CAGR is approximately 24.8%.
2. Which companies are prominent players in the iot identity access management iam?
Key companies in the market include Global and United States.
3. What are the main segments of the iot identity access management iam?
The market segments include Application, Types.
4. Can you provide details about the market size?
The market size is estimated to be USD XXX N/A as of 2022.
5. What are some drivers contributing to market growth?
N/A
6. What are the notable trends driving market growth?
N/A
7. Are there any restraints impacting market growth?
N/A
8. Can you provide examples of recent developments in the market?
N/A
9. What pricing options are available for accessing the report?
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 4350.00, USD 6525.00, and USD 8700.00 respectively.
10. Is the market size provided in terms of value or volume?
The market size is provided in terms of value, measured in N/A.
11. Are there any specific market keywords associated with the report?
Yes, the market keyword associated with the report is "iot identity access management iam," which aids in identifying and referencing the specific market segment covered.
12. How do I determine which pricing option suits my needs best?
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
13. Are there any additional resources or data provided in the iot identity access management iam report?
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
14. How can I stay updated on further developments or reports in the iot identity access management iam?
To stay informed about further developments, trends, and reports in the iot identity access management iam, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.
Methodology
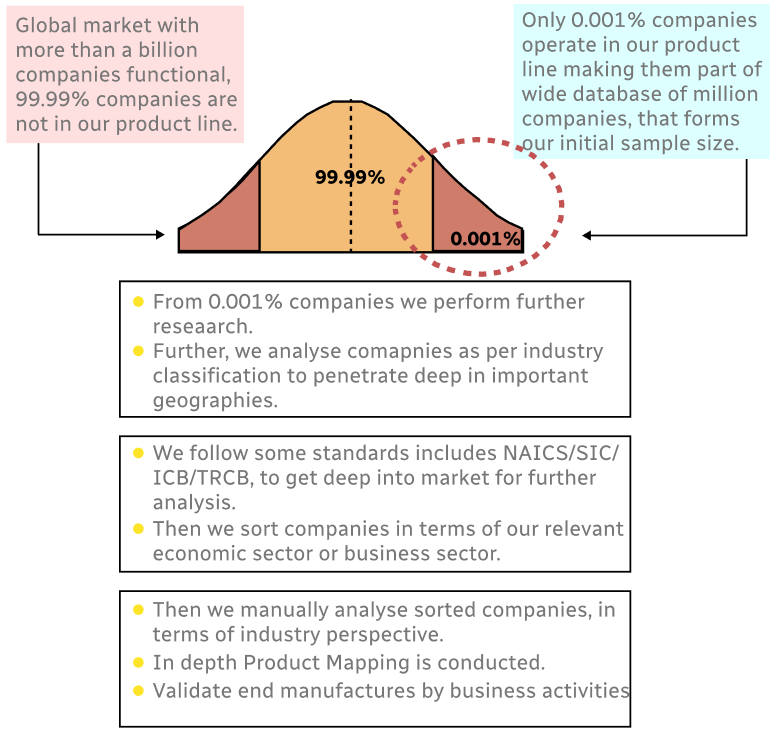
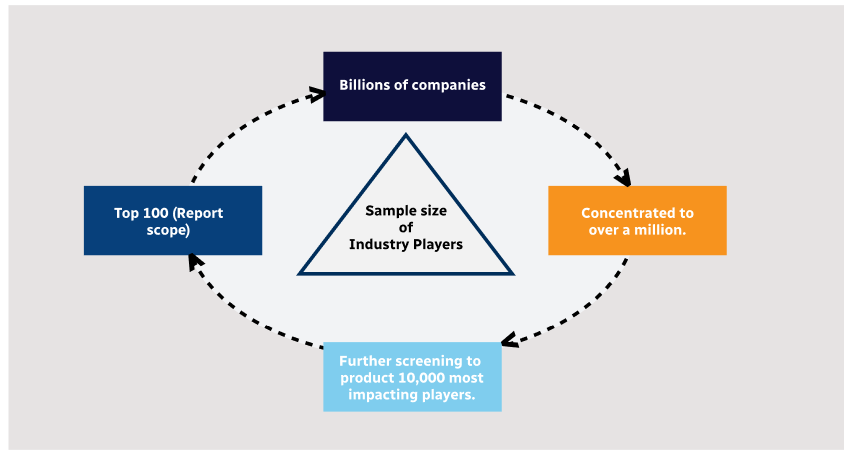
Step 1 - Identification of Relevant Samples Size from Population Database
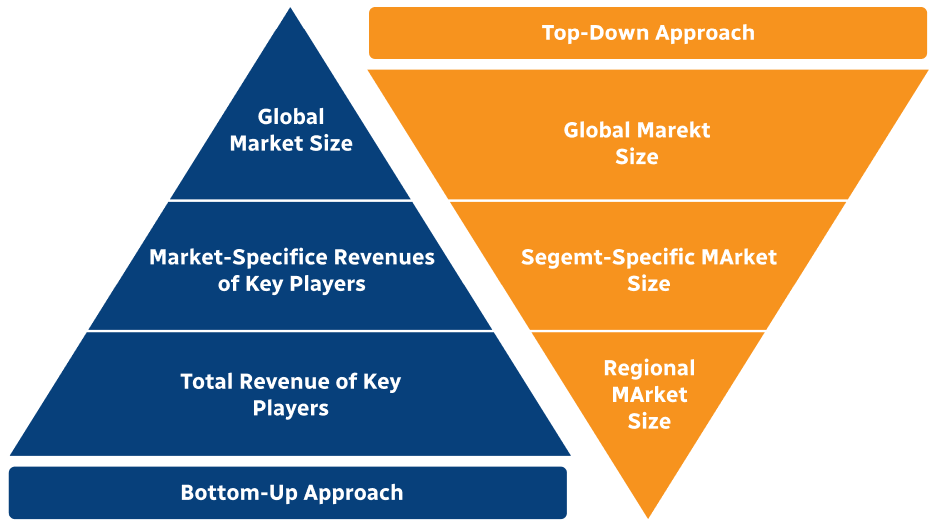
Step 2 - Approaches for Defining Global Market Size (Value, Volume* & Price*)
Note*: In applicable scenarios
Step 3 - Data Sources
Primary Research
- Web Analytics
- Survey Reports
- Research Institute
- Latest Research Reports
- Opinion Leaders
Secondary Research
- Annual Reports
- White Paper
- Latest Press Release
- Industry Association
- Paid Database
- Investor Presentations
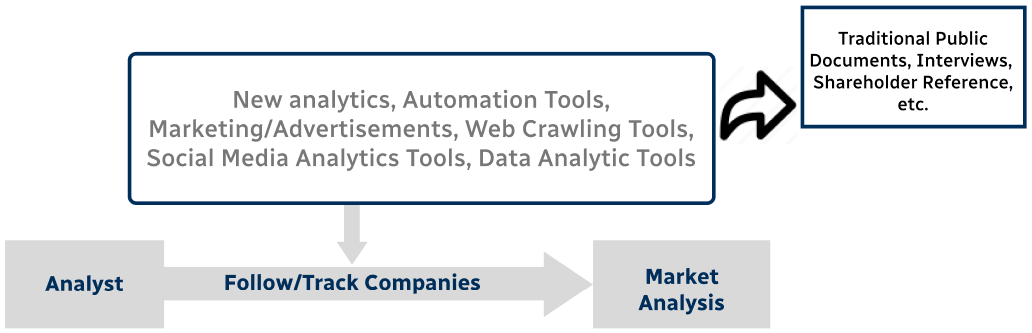
Step 4 - Data Triangulation
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence